How Can Ppl Say Cats Are Heartless Tbh
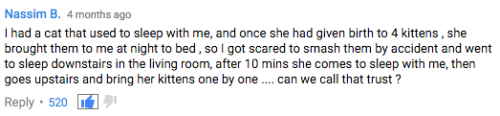
how can ppl say cats are heartless tbh
More Posts from Sumactic and Others
She deserves all the pets

Cybercriminals are abusing Google’s infrastructure, creating emails that appear to come from Google in order to persuade people into handing over their Google account credentials. This attack, first flagged by Nick Johnson, the lead developer of the Ethereum Name Service (ENS), a blockchain equivalent of the popular internet naming convention known as the Domain Name System (DNS). Nick received a very official looking security alert about a subpoena allegedly issued to Google by law enforcement to information contained in Nick’s Google account. A URL in the email pointed Nick to a sites.google.com page that looked like an exact copy of the official Google support portal.
As a computer savvy person, Nick spotted that the official site should have been hosted on accounts.google.com and not sites.google.com. The difference is that anyone with a Google account can create a website on sites.google.com. And that is exactly what the cybercriminals did. Attackers increasingly use Google Sites to host phishing pages because the domain appears trustworthy to most users and can bypass many security filters. One of those filters is DKIM (DomainKeys Identified Mail), an email authentication protocol that allows the sending server to attach a digital signature to an email. If the target clicked either “Upload additional documents” or “View case”, they were redirected to an exact copy of the Google sign-in page designed to steal their login credentials. Your Google credentials are coveted prey, because they give access to core Google services like Gmail, Google Drive, Google Photos, Google Calendar, Google Contacts, Google Maps, Google Play, and YouTube, but also any third-party apps and services you have chosen to log in with your Google account. The signs to recognize this scam are the pages hosted at sites.google.com which should have been support.google.com and accounts.google.com and the sender address in the email header. Although it was signed by accounts.google.com, it was emailed by another address. If a person had all these accounts compromised in one go, this could easily lead to identity theft.
How to avoid scams like this
Don’t follow links in unsolicited emails or on unexpected websites.
Carefully look at the email headers when you receive an unexpected mail.
Verify the legitimacy of such emails through another, independent method.
Don’t use your Google account (or Facebook for that matter) to log in at other sites and services. Instead create an account on the service itself.
Technical details Analyzing the URL used in the attack on Nick, (https://sites.google.com[/]u/17918456/d/1W4M_jFajsC8YKeRJn6tt_b1Ja9Puh6_v/edit) where /u/17918456/ is a user or account identifier and /d/1W4M_jFajsC8YKeRJn6tt_b1Ja9Puh6_v/ identifies the exact page, the /edit part stands out like a sore thumb. DKIM-signed messages keep the signature during replays as long as the body remains unchanged. So if a malicious actor gets access to a previously legitimate DKIM-signed email, they can resend that exact message at any time, and it will still pass authentication. So, what the cybercriminals did was: Set up a Gmail account starting with me@ so the visible email would look as if it was addressed to “me.” Register an OAuth app and set the app name to match the phishing link Grant the OAuth app access to their Google account which triggers a legitimate security warning from no-reply@accounts.google.com This alert has a valid DKIM signature, with the content of the phishing email embedded in the body as the app name. Forward the message untouched which keeps the DKIM signature valid. Creating the application containing the entire text of the phishing message for its name, and preparing the landing page and fake login site may seem a lot of work. But once the criminals have completed the initial work, the procedure is easy enough to repeat once a page gets reported, which is not easy on sites.google.com. Nick submitted a bug report to Google about this. Google originally closed the report as ‘Working as Intended,’ but later Google got back to him and said it had reconsidered the matter and it will fix the OAuth bug.




Few more 🌱
first part here second part here based on a book about Czech forests (Naše pralesy)
In the end, I've decided to sell all the original drawings from this forest series! Prices from 60 to 80USD (shipping included) - all the earnings will be sent to charities. If anyone's interested, you can reserve them now by sending me a message or an email (s.u.w.i@email.cz), thanks! All taken!
the framing of generative ai as "theft" in popular discourse has really set us back so far like not only should we not consider copyright infringement theft we shouldn't even consider generative ai copyright infringement
reddit, how do I make my firstborn stop playing with the fans, the ornaments, and the makeup when he is supposed to be a warlord. I fear I shall raise a poet.
Writing mcyt fanfic feels so silly because the names are on a spectrum from "normal human name" to "semi-plausible" to "Sausage"
![a graphic design of an imaginary sign in an upper class area, perhaps a university. the sign reads: "[acid hazard symbol]. WARNING. THIS AREA IS MONITORED AND REGULARLY MISTED WITH CORROSIVE ACID TO DETER LOITERING. [no skateboarding, no sitting, and no tents symbols]. Thank you for keeping Our City Clean™"](https://64.media.tumblr.com/63a98c5ebeba04e050ae2a020843c8cd/2d9b904f2636ac48-c3/s500x750/c98eddb31ea75d2398bb3c9e6f22110b618091bb.png)
loaf with mama



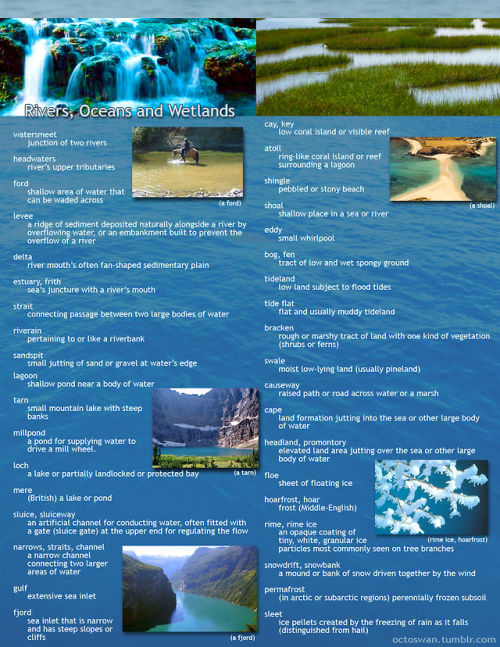
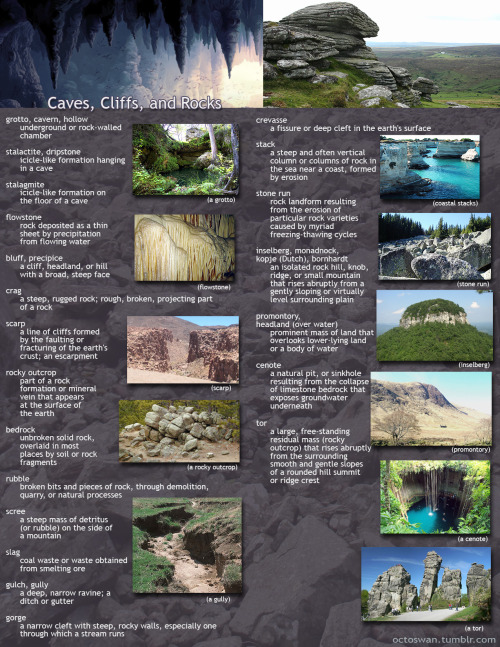
I made these as a way to compile all the geographical vocabulary that I thought was useful and interesting for writers. Some descriptors share categories, and some are simplified, but for the most part everything is in its proper place. Not all the words are as useable as others, and some might take tricky wording to pull off, but I hope these prove useful to all you writers out there!
(save the images to zoom in on the pics)
The most frustrating part of being trans is that you can't win.
My uni has quite a few all-gender washrooms. (Specifically all-gender, cis people are absolutely encouraged to use them). And despite the fact that there are womens washrooms everywhere on campus as well, I've had cis women treat me with borderline disgust when I use the all-gender bathroom. I've had people tell me that "sure, its all genders, but when a cis man uses it its just weird".
And like. Thats the point! Even IF a cishet man using a washroom he is specifically allowed in was weird. Even then. You have to understand that no trans or nonbinary person can safely use an all-genders washroom if using it means they are either trans or female.
Like to be very clear- I am a cis-passing trans man. There are so many reasons I feel more comfortable in a non-gendered washroom. Even if I was cis I woild likely want to, because I am gnc and don't always feel safe in purely male spaces. And even if I was the cissest, hetesst, most gender conforming man on the planet, I might still want to use it because its closer to my classes.
And really, this all comes back to this deeply transmisoginistic idea that Men Are A Threat to Women in Womens Washrooms,, which. If I have to explain to you why this is purely a propagandistic falsehood I really think you need to do a gender 101 course.
Gender neutral washrooms cannot be "women Lite washrooms". In order to protect trans people, at all stages of coming out and transition and of all presentations, for the love of god stop dictating who can use all-gender washrooms.
-
 meandtherodentinthewall reblogged this · 2 weeks ago
meandtherodentinthewall reblogged this · 2 weeks ago -
 scientifichydralisk liked this · 2 weeks ago
scientifichydralisk liked this · 2 weeks ago -
 silvertongue21 reblogged this · 2 weeks ago
silvertongue21 reblogged this · 2 weeks ago -
 silvertongue21 liked this · 2 weeks ago
silvertongue21 liked this · 2 weeks ago -
 vivisoloperte liked this · 2 weeks ago
vivisoloperte liked this · 2 weeks ago -
 thearacanemystery liked this · 2 weeks ago
thearacanemystery liked this · 2 weeks ago -
 vivienneperseus liked this · 2 weeks ago
vivienneperseus liked this · 2 weeks ago -
 artandanimationaddiction liked this · 2 weeks ago
artandanimationaddiction liked this · 2 weeks ago -
 sortofshea liked this · 2 weeks ago
sortofshea liked this · 2 weeks ago -
 darthxochitl liked this · 2 weeks ago
darthxochitl liked this · 2 weeks ago -
 heavy-metal-dick reblogged this · 2 weeks ago
heavy-metal-dick reblogged this · 2 weeks ago -
 lifelovelaughterlarry liked this · 2 weeks ago
lifelovelaughterlarry liked this · 2 weeks ago -
 carliethehufflepuff liked this · 2 weeks ago
carliethehufflepuff liked this · 2 weeks ago -
 dollydollspookprincess reblogged this · 2 weeks ago
dollydollspookprincess reblogged this · 2 weeks ago -
 dollydollspookprincess liked this · 2 weeks ago
dollydollspookprincess liked this · 2 weeks ago -
 itsstupidtime reblogged this · 2 weeks ago
itsstupidtime reblogged this · 2 weeks ago -
 itsstupidtime liked this · 2 weeks ago
itsstupidtime liked this · 2 weeks ago -
 hallo-spaceb0y reblogged this · 2 weeks ago
hallo-spaceb0y reblogged this · 2 weeks ago -
 hallo-spaceb0y liked this · 2 weeks ago
hallo-spaceb0y liked this · 2 weeks ago -
 glass-snow liked this · 2 weeks ago
glass-snow liked this · 2 weeks ago -
 lunar-wraith reblogged this · 2 weeks ago
lunar-wraith reblogged this · 2 weeks ago -
 random-shit-writing liked this · 2 weeks ago
random-shit-writing liked this · 2 weeks ago -
 slademore liked this · 2 weeks ago
slademore liked this · 2 weeks ago -
 dangerousbleus reblogged this · 2 weeks ago
dangerousbleus reblogged this · 2 weeks ago -
 iamnmbr3 reblogged this · 2 weeks ago
iamnmbr3 reblogged this · 2 weeks ago -
 sumactic reblogged this · 2 weeks ago
sumactic reblogged this · 2 weeks ago -
 robyn-goodfellowe liked this · 3 weeks ago
robyn-goodfellowe liked this · 3 weeks ago -
 alabastermask reblogged this · 3 weeks ago
alabastermask reblogged this · 3 weeks ago -
 narrenmat reblogged this · 3 weeks ago
narrenmat reblogged this · 3 weeks ago -
 2003s-greatest-horrorshow liked this · 3 weeks ago
2003s-greatest-horrorshow liked this · 3 weeks ago -
 moonmacabre01 reblogged this · 4 weeks ago
moonmacabre01 reblogged this · 4 weeks ago -
 endorphinjohnsonjohnson liked this · 4 weeks ago
endorphinjohnsonjohnson liked this · 4 weeks ago -
 depressed-pheldritch-horror reblogged this · 1 month ago
depressed-pheldritch-horror reblogged this · 1 month ago -
 depressed-pheldritch-horror liked this · 1 month ago
depressed-pheldritch-horror liked this · 1 month ago -
 thinkingisadangerouspastime reblogged this · 1 month ago
thinkingisadangerouspastime reblogged this · 1 month ago -
 ilikesocks101 liked this · 1 month ago
ilikesocks101 liked this · 1 month ago -
 metrickulous reblogged this · 1 month ago
metrickulous reblogged this · 1 month ago -
 ss-dazy reblogged this · 1 month ago
ss-dazy reblogged this · 1 month ago -
 romance-hominum liked this · 1 month ago
romance-hominum liked this · 1 month ago -
 suspiciouslyqueeraardvark reblogged this · 1 month ago
suspiciouslyqueeraardvark reblogged this · 1 month ago -
 lolanbq reblogged this · 1 month ago
lolanbq reblogged this · 1 month ago -
 forlorn-findings reblogged this · 1 month ago
forlorn-findings reblogged this · 1 month ago -
 noiwillnotshutup reblogged this · 1 month ago
noiwillnotshutup reblogged this · 1 month ago -
 naiadbookworm liked this · 1 month ago
naiadbookworm liked this · 1 month ago -
 decrepit-furby reblogged this · 1 month ago
decrepit-furby reblogged this · 1 month ago -
 adrianaalvz64 liked this · 1 month ago
adrianaalvz64 liked this · 1 month ago -
 lhylice reblogged this · 1 month ago
lhylice reblogged this · 1 month ago -
 lhylice liked this · 1 month ago
lhylice liked this · 1 month ago -
 champ-wiggle reblogged this · 1 month ago
champ-wiggle reblogged this · 1 month ago